New: Flexible service plans for Myra WAF. Learn more!
Home>
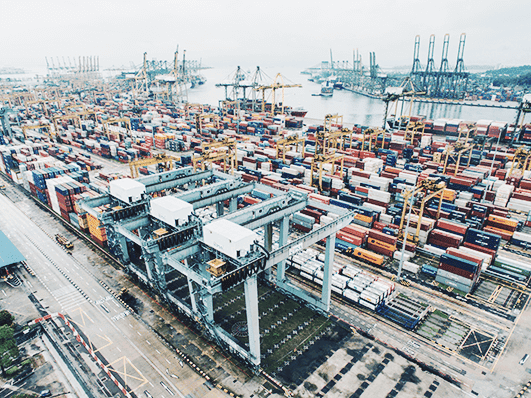
Transportation & Logistics

Myra Security offers custom solutions
for the transportation and logistics industry

Comprehensively certified
ISO 27001 based on BSI IT-Grundschutz, PCI-DSS, IDW PS 951 (ISAE 3402), Trusted Cloud, BSI C5 typ 2

Audited
GDPR and IT-SiG compliant, BSI-KRITIS certified

Security Operations Center
24/7 full-service support from our IT specialists

High scalability
Quick installation and easy operation

Made in Germany
Development and operation entirely in Germany

Many years of experience
Myra specializes in the protection of critical infrastructure






Our technologies for protecting the transportation and logistics sector
Myra DDoS Web Protection automatically protects online tools, websites, and the DNS servers and IT infrastructure required for communication. Myra meets all the performance requirements defined by the German Federal Office for Information Security (BSI) for qualified DDoS protection providers. As such, highly sensitive infrastructure is in safe hands with Myra.
About Myra DDoS Web ProtectionAs an upstream filter, Myra Application Security protects your web applications. Malicious traffic is filtered before it reaches your servers or cloud architecture. Using Myra’s multi-fingerprinting features, any applications attempting access are clearly identified and displayed in Myra Analytics.
About Myra Application SecurityDo you have
questions?
Please contact us via contact form or call us at:
+49 89 414141 - 345.