New: Flexible service plans for Myra WAF. Learn more!
Home>
Bot
02
Types of bots
Bots are used for both legal and illegal purposes. In the following we will introduce you to some of the most common representatives of this type of software. The spectrum ranges from simple business tools, bots for gaming and social media, to malicious spam bots.
Web crawlers
Indexing websites is the basis for how search engines like Google or Bing work. Only by using web crawlers, which analyze and index URLs, is it at all possible to sort and present search results. These bots independently scour the internet for relevant content to list on search services.
Chatbots
Particularly in e-commerce, companies increasingly rely on chatbots for customer support. The automated helpers provide answers to the most relevant questions and support customers when shopping or troubleshooting. For more complex topics, the customer is usually referred to conventional customer support. This enables companies to lower the workload of their own service teams and provide cost-effective 24/7 support for their customers.
Social bots
Social bots, as the name implies, are mainly used in social networks such as Facebook or Twitter. Here, the tools perform a variety of tasks:
Publishing content for a page or a user.
Automatically liking and commenting on Facebook posts or retweeting and commenting on tweets.
Interactive user communication as a chatbot. However, this application is not allowed in the terms and conditions of most social networks.
Trading bots
Bots are also used to trade digital currency. The prices of Bitcoin and other cryptocurrencies are extremely volatile, so it makes sense to continuously monitor your own investment. Since no one can do this from an economic standpoint, trading bots handle this task.
Game bots
We also encounter bots in computer games, mostly as NPCs (non-player characters). They are computer-controlled players or opponents in PC games. In online role-playing games, there are other types of game bots that players employ to perform monotonous tasks, such as collecting resources or experience points. However, most games do not allow the use of such bots and ban players who use them.
Email-Bots
Similar to chat bots, email bots manage conversations with customers and prospects. Email bots can be integrated into existing email automation platforms and take over part of email communication. These mailing tools are particularly suitable for simple support or contact requests.
Spam bots
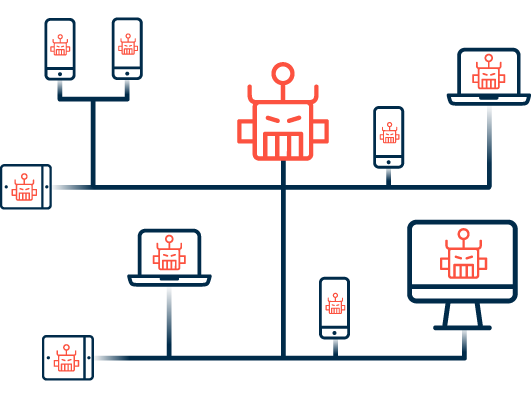
Cybercriminals sometimes use bots to send spam e-mail. They use email harvesters that automatically scan websites for publicly accessible addresses. The fraudsters then sell these mass-aggregated addresses for a profit on the darknet or use them themselves as targets for spam campaigns. The actual sending is also usually done using bots or botnets.
04
Opportunities and threats for companies
Chatbots on their own website as well as email bots are being increasingly used by a growing number of companies to simplify and enliven communication with their customers and prospects. They are popular marketing instruments and represent an opportunity, especially in customer acquisition. Malicious bots, on the other hand, pose a threat to companies that should not be underestimated. They harm SEO rankings, slow down webshops and are used in combination as a botnet for DDoS attacks.
Want to learn more about our solutions, use cases and best practices for attack defense? In our download area you will find product sheets, fact sheets, white papers and case studies.
About the author
Stefan Bordel
Senior Editor
About the author
Stefan Bordel has been working as an editor and technical writer at Myra Security since 2020. In this role, he is responsible for creating and maintaining website content, reports, whitepapers, social media content and documentation. This role allows him to bring his extensive experience in IT journalism and technical knowledge to an innovative cyber security company. Stefan previously worked at Ebner Verlag (formerly Neue Mediengesellschaft Ulm) for 7 years and joined the online editorial team at com! professional after working for Telecom Handel. He gained his first journalistic experience during various internships, including at the IT website Chip Online. As a passionate Linux user, he follows the IT scene closely, both privately and professionally.