New: Flexible service plans for Myra WAF. Learn more!
Home>
Patch
01
A definition of a patch
A patch is a set of software changes that quickly resolves a bug or security vulnerability in software currently in use. A patch is also called a “fix” or “bugfix.” It dates back to the time when data was stored on punched cards: at that time, patches were used to “patch in” individual holes cut out in punched cards. Available patches are usually offered for download on the software manufacturer’s website or are installed automatically (or with consent) to the software. A changelog, which is often included, can be used to track exactly which bugs have been fixed.
For business software or operating systems such as Windows, a special management program is typically used to install patches. Many applications and operating systems have fixed update and patch cycles. For example, Microsoft usually releases patches for its products on the second Tuesday of each month, known as “Patch Tuesday.” The reason for this is to make it easier for administrators to plan and install updates. However, critical security patches are also made available outside the regular update cycle.
05
What should companies consider when patching?
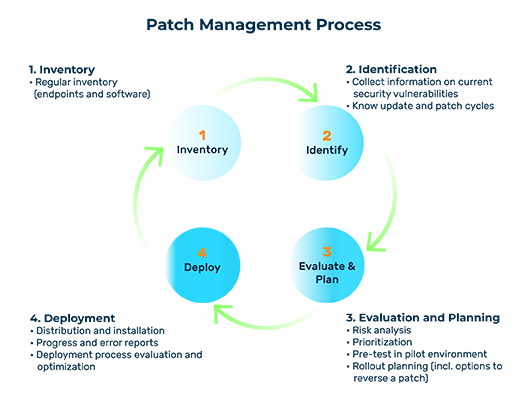
Good planning and clear processes when it comes to patching are the be-all and end-all for minimizing many cyber risks, especially when it comes to companies. IT departments should follow a clearly defined patch management process and keep track of the different measures required when patching.
Inventory management
It starts with an inventory to get an overview of the number and type of all endpoints (laptops, PCs, servers, and other devices) and the software installed on them.
Identification
The second step is to continuously monitor information about current security vulnerabilities and threats. The update and patch cycles of the software used should also be known.
Evaluation and planning
In the subsequent evaluation and planning phase, a risk analysis and prioritization must be carried out to determine which systems are currently most at risk and therefore need to be patched first. Because patching during live operation is always associated with risks such as malfunctions and system failures, it is advisable to conduct preliminary tests in a pilot environment. It is also possible to create a certain degree of protection with the help of rollback plans and recovery options in the event of malfunctions or compatibility problems.
Deployment
Once the rollout has been planned, the patches can be distributed and installed. Afterward, the effects must be checked in detail to assess whether the process was successful. A final evaluation of the deployment process allows it to be continuously optimized.
Using a patch management platform, necessary patches can be installed and monitored centrally and throughout the company. An automated patch management system independently checks software used in the company for vulnerabilities and provides information about available security updates, which are then installed automatically. Not only does this make the patching process more efficient, but it also makes it faster. Every minute counts, especially when there is an acute threat. Reports can be checked to verify the success of the installation. If something goes wrong and a patch causes unexpected problems, it can be reversed by the patch management solution.
Want to learn more about our solutions, use cases and best practices for attack defense? In our download area you will find product sheets, fact sheets, white papers and case studies.
About the author
Stefan Bordel
Senior Editor
About the author
Stefan Bordel has been working as an editor and technical writer at Myra Security since 2020. In this role, he is responsible for creating and maintaining website content, reports, whitepapers, social media content and documentation. This role allows him to bring his extensive experience in IT journalism and technical knowledge to an innovative cyber security company. Stefan previously worked at Ebner Verlag (formerly Neue Mediengesellschaft Ulm) for 7 years and joined the online editorial team at com! professional after working for Telecom Handel. He gained his first journalistic experience during various internships, including at the IT website Chip Online. As a passionate Linux user, he follows the IT scene closely, both privately and professionally.