New: Flexible service plans for Myra WAF. Learn more!
Home>
Low Orbit Ion Cannon
At one look
- 01. Low Orbit Ion Cannon: Definition
- 02. How does Low Orbit Ion Cannon work?
- 03. Is the Low Orbit Ion Cannon legal?
- 04. Are there any known examples of attacks using Low Orbit Ion Cannon?
- 05. How can you defend against traffic overload attacks by Low Orbit Ion Cannon?
- 06. Low Orbit Ion Cannon: What do you need to know?
03
Is the Low Orbit Ion Cannon legal?
The stress test tool itself is legal and freely available on the Internet. It should be noted, however, that it is only legal to perform load tests on your own IT infrastructures. Unauthorized use of the Low Orbit Ion Cannon against third-party targets violates the laws of most countries. In Germany, this is considered computer sabotage under § 303b StGB (German Criminal Code) and is subject to criminal prosecution. Attackers face fines and/or several years in prison.
Those who use LOIC for illegal overload attacks should expect to be quickly identified and prosecuted. Such attacks leave the IP addresses of the attackers visible to the target and they cannot be disguised via a proxy server, as the attack would otherwise hit the proxy instead of the actual target.
04
Are there any known examples of attacks using Low Orbit Ion Cannon?
The Low Orbit Ion Cannon was primarily used by the hacker collective Anonymous and members of the 4chan forum for several noteworthy DDoS attacks:
Project Chanology
In early 2008, Anonymous, together with supporters from the 4chan forum, used the LOIC for a series of DDoS attacks on Scientology websites. The hacker collective took this action in response to a copyright lawsuit filed against Youtube by the Church of Scientology. The Scientology organization had demanded that the video service and other websites delete a leaked video featuring actor Tom Cruise.
Operation Payback
Beginning in September 2010, Anonymous conducted multiple DDoS attacks against the websites of financial institutions, industry associations, and government agencies as part of “Operation Payback” using Low Orbit Ion Cannon. The hacker collective used these attacks to protest against the closure of the torrent site Pirate Bay and the blocking of Wikileaks’ donation account. The attacks were directed at the Motion Picture Association of America, the Recording Industry Association of America and the U.S. Copyright Office, among others. Later, Bank of America, Paypal and credit card companies such as Visa and Mastercard were also affected after they refused to forward donations to the whistleblower organization Wikileaks.
Operation Megaupload
In early 2012, Anonymous initiated DDoS attacks via LOIC in response to the closure of the file hosting company Megaupload. Targets included the websites of the FBI, the U.S. Department of Justice, U.S. film and music industry associations, and several record labels. According to the hacker collective, it was its largest attack campaign ever up to that point – a total of 5,635 people with their own LOIC instance are said to have participated.
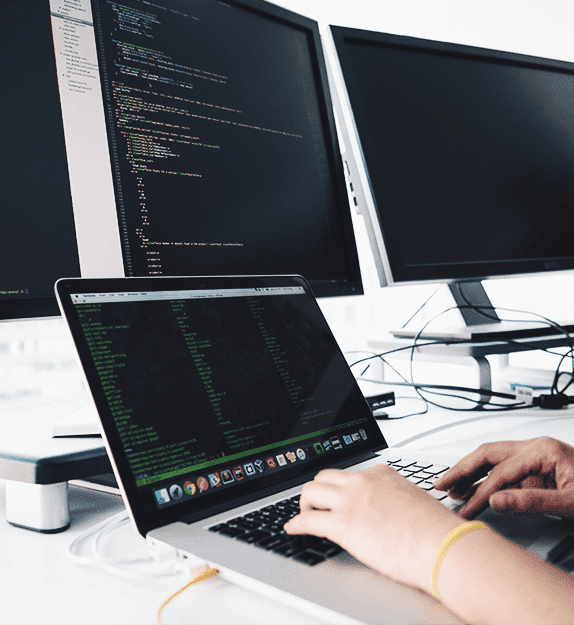
Cybersecurity Solutions by Myra

DDoS Protection
Myra DDoS Protection provides you with fully automatic protection against malicious requests and overload attacks. Even in the event of an imminent attack, your web applications stay available at all times.
Hyperscale WAF
The Myra Hyperscale WAF protects your web applications against malicious access and vulnerability exploits. Thanks to simple integration and configuration, it can be set up in no time at all.
CDN
First-class user experience thanks to fast page loading and minimal latency: With the Myra High Performance CDN, all static and dynamic content on your website is delivered with high performance.
Secure DNS
Myra Secure DNS offers you a reliable and powerful solution for securing your critical web applications. Manage your name resolution with ease and protect yourself against DNS hijacking.
Deep Bot Management
Say goodbye to malicious bots forever. Myra Deep Bot Management creates unique fingerprints for each bot and thus enables an optimal response to every request.
Certificate Management
No more problems with expired SSL/TLS certificates. Increase the security of your digital assets with Myra Certificate Management and encrypt all your domains automatically.
Want to learn more about our solutions, use cases and best practices for attack defense? In our download area you will find product sheets, fact sheets, white papers and case studies.
About the author
Björn Greif
Senior Editor
About the author
Björn started his career as an editor at the IT news portal ZDNet in 2006. 10 years and exactly 12,693 articles later, he joined the German start-up Cliqz to campaign for more privacy and data protection on the web. It was then only a small step from data protection to IT security: Björn has been writing about the latest trends and developments in the world of cybersecurity at Myra since 2020.